The Of Risk Management Enterprise
Table of ContentsThe Only Guide to Risk Management EnterpriseRisk Management Enterprise Fundamentals ExplainedFacts About Risk Management Enterprise RevealedAn Unbiased View of Risk Management EnterpriseIndicators on Risk Management Enterprise You Should KnowThe Facts About Risk Management Enterprise UncoveredGetting My Risk Management Enterprise To Work
Here are some of its essential functions that facilities need to recognize. Take a look. Real-Time Threat Analyses and Reduction in this software application allow companies to continuously monitor and assess dangers as they develop. This feature leverages real-time information and automatic evaluation to recognize possible threats without delay. Once dangers are recognized, the software helps with prompt reduction activities.
KRIs solve the issue of inconsistent or unclear threat analysis. They address the obstacle of continuous threat administration by offering tools to check dangers constantly. KRIs boost safety risk oversight, making certain that possible dangers are identified and taken care of properly. The job of risk monitoring need to not be a challenge. Therefore, organizations need to count on a top-notch and innovative danger management software.
Get This Report about Risk Management Enterprise
IT run the risk of management is a subset of business danger management (ERM), designed to bring IT take the chance of in accordance with a company's threat appetite. IT take the chance of management (ITRM) incorporates the plans, treatments and modern technology essential to minimize threats and vulnerabilities, while preserving compliance with suitable regulative demands. Additionally, ITRM looks for to restrict the effects of harmful occasions, such as protection violations.
While ITRM structures provide useful assistance, it's easy for IT teams to experience "framework overload." Veronica Rose, ISACA board director and a details systems auditor at Metropol Corp. Ltd., advises using a combination of frameworks to achieve the very best outcomes. As an example, the ISACA Risk IT framework straightens well with the COBIT 2019 structure, Rose claimed.
Business Risk Management Software Program Growth: Benefits & Features, Expense. With technological innovations, risks are continually on the increase., services browse with a constantly transforming sea of dangers.
Getting The Risk Management Enterprise To Work
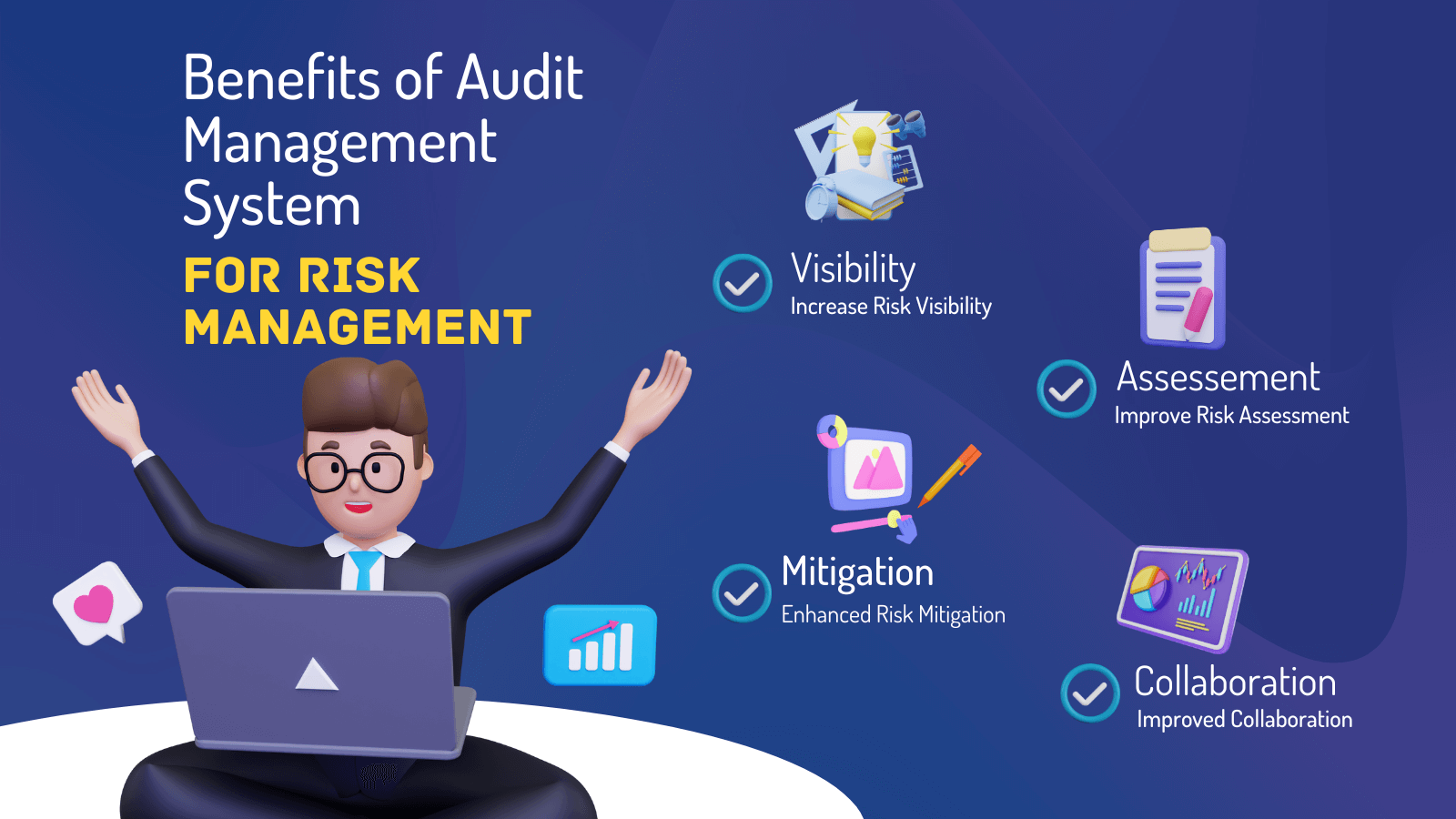
In this blog, we will study the globe of ERM software program, discovering what it is, its benefits, attributes, etc to ensure that you can construct one for your organization. Venture Threat Management (ERM) software application is the application program for planning, directing, arranging, and regulating organization tasks and enhancing threat management processes.
With ERM, organizations can make informative decisions to enhance the overall durability of the service. Dedicated ERM systems are important for organizations that consistently deal with substantial quantities of delicate information and several stakeholders to accept tactical decisions.
It can be avoided by utilizing the ERM software program system. This system automates guideline conformity monitoring to maintain the company safe and compliant.
All About Risk Management Enterprise
You can additionally connect existing software program systems to the ERM via APIs or by adding data manually. Organizations can utilize ERM to evaluate threats based on their prospective effect for far better threat management and mitigation.: Adding this feature enables individuals to get real-time alerts on their tools about any kind of threat that could take place and its influence.
Instead, the software allows them to set limits for various processes and send press notifications in situation of possible threats.: By incorporating information visualization and reporting in the custom-made ERM software application, organizations can gain clear understandings about risk trends and performance.: It is mandatory for organizations to follow sector compliance and regulative standards.
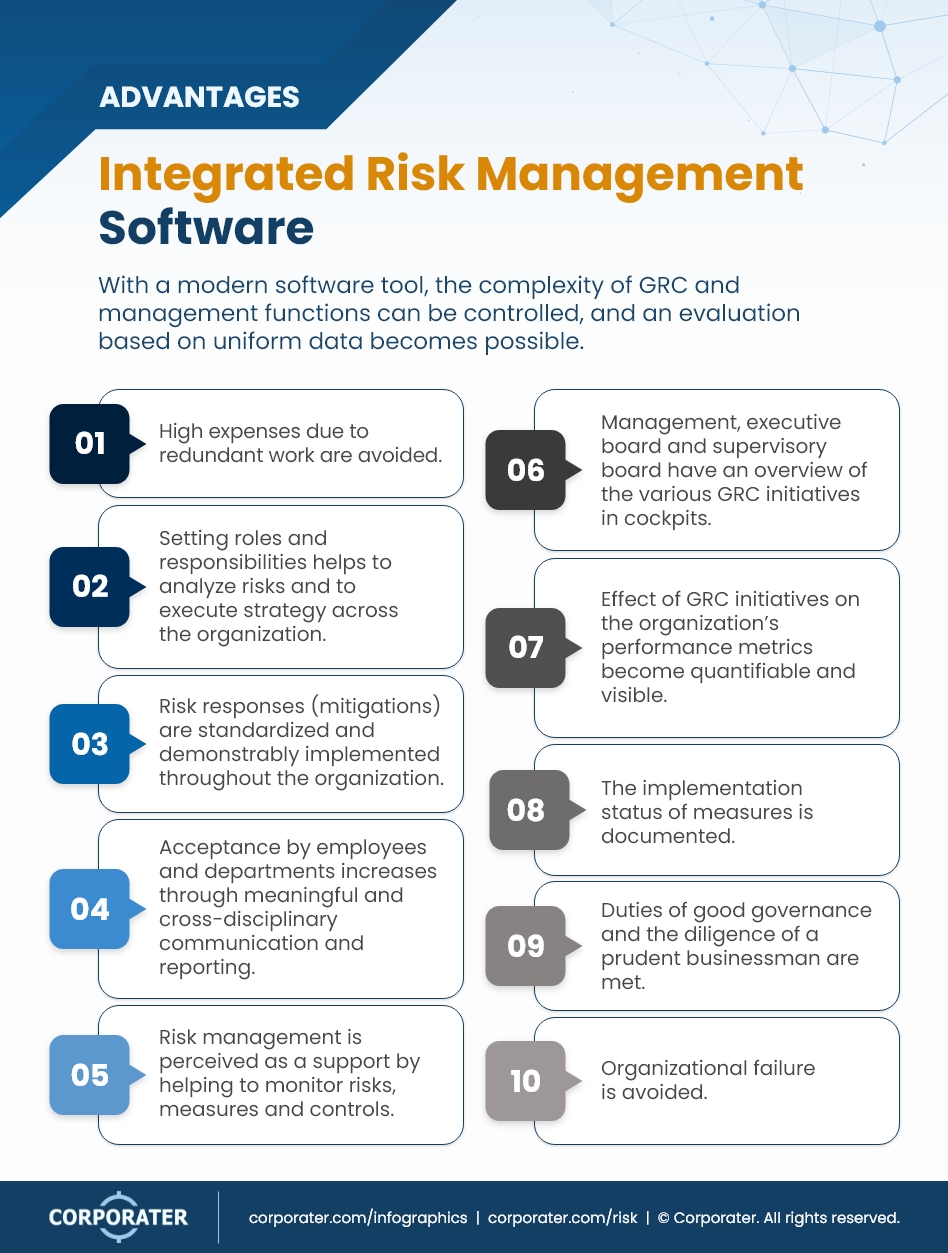
These systems make it possible for firms to execute best-practice danger management processes that line up with market standards, using a powerful, technology-driven strategy to identifying, evaluating, and mitigating dangers. This blog discovers the benefits of automated threat management tools, the visit homepage areas of danger management they can automate, and the value they give an organization.
All About Risk Management Enterprise
Teams can establish up types with the appropriate areas and easily produce various forms for different danger kinds. These risk assessment kinds can be flowed for completion through automated workflows that send notifications to the pertinent team to complete the kinds online. If forms are not completed by the due date, then chaser e-mails are instantly sent out by the system.
The control tracking and control testing procedure can likewise be automated. Firms can use automated workflows to send out normal control test alerts and staff can enter the results via online types. Controls can likewise be kept an eye on by the software application by setting guidelines to send out alerts based on control information kept in other systems and spreadsheets that is pulled into the platform using API combinations.
Risk management automation software can additionally support with danger coverage for all degrees of the business. Leaders can check out records on threat direct exposure and control performance via a range of reporting results including fixed records, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The ability to pull actual time records at the touch of a button eliminates difficult data adjustment tasks leaving danger groups with even more time to analyze find the data and advise the company on the very best strategy.
Organizations operating in competitive, fast-changing markets can't afford delays or inadequacies in dealing with possible dangers. Conventional danger management making use of hands-on spreadsheet-based procedures, while acquainted, frequently lead to fragmented information, lengthy coverage, and a raised likelihood of human error.
The 10-Minute Rule for Risk Management Enterprise
This ensures threat signs up are constantly current and straightened with business objectives. Compliance is an additional critical driver for automating threat monitoring. Standards like ISO 31000, CPS 230 and COSO all provide guidance around risk administration finest methods and control frameworks, and automated threat administration devices are structured to line up with these needs helping firms to fulfill most frequently used danger monitoring criteria.
Seek risk software application platforms with a permissions pecking order to conveniently establish operations for danger rise. This functionality allows you to tailor the view Look At This for every customer, so they only see the data pertinent to them. Make sure the ERM software program uses customer monitoring so you can see that entered what data and when.
Seek out tools that provide project danger administration abilities to manage your jobs and profiles and the linked risks. The benefits of taking on risk monitoring automation software expand much beyond efficiency.
Things about Risk Management Enterprise
While the instance for automation is engaging, implementing a danger monitoring system is not without its difficulties. To overcome the challenges of risk monitoring automation, companies should invest in data cleaning and governance to ensure a solid foundation for implementing an automated platform.
Automation in risk administration equips businesses to change their method to risk and develop a more powerful foundation for the future (Risk Management Enterprise). The question is no much longer whether to automate risk monitoring, it's exactly how quickly you can start. To see the Riskonnect in action,
The response often exists in how well dangers are expected and handled. Project management software application serves as the navigator in the turbulent waters of job implementation, offering tools that determine and analyze threats and develop approaches to mitigate them efficiently.